- Solutions
- Products
- StealthAUDITReporting & Governance
- ---
- Stealthbits App Catalog Browse our catalog of no-charge resource connectors, report packs, and more.
- ---
- StealthDEFENDThreat Detection & Response
- ---
- SbPAMPrivileged Access Management
- ---
- StealthINTERCEPTPolicy Enforcement
- ---
- StealthRECOVERRoll Back & Recovery
- StealthAUDIT
- Support
- Partners
- Company
- Resources
- Login
- Free Trial
Stealthbits
Posts by Kevin Joyce
Active Directory Permissions – Hiding in the Shadows
Understanding the Risk of Active Directory Permissions and Shadow Access I recently covered the topic of Active Directory permissions by giving an overview on how to apply them and view what already exists in your organization. In this blog, I’ll be taking a deeper dive into Active Directory permissions, outlining potential risks that exist when […]

SMBv3 Vulnerability Explained
SMBGhost What Happened? This week, Microsoft accidentally published information around a newly identified vulnerability in SMBv3, which is being dubbed SMBGhost. This vulnerability can lead to remote code execution on the server, which is always a major concern as far as the severity of vulnerabilities go. The version affected specifically is 3.1.1, which is a […]

Ready for Microsoft’s LDAP Changes? What You Need to Know
What is Changing? In March, Microsoft will be releasing a patch that includes new audit events, additional logging, and some changes to group policy settings. Later in 2020, Microsoft will be changing the behavior of the default values for LDAP channel binding and signing. They’re making these changes because the current default settings allow for […]

What is SMBv1 and Why You Should Disable it
Eternally Affected What is SMB? Server Message Block (SMB) is a protocol used primarily for sharing files, printer services, and communication between computers on a network. The history of SMB is long, so I’ll try to keep this short and to the point. SMBv1 Back in the 1980s and 1990s IBM and Microsoft were working […]

What is Kerberos Delegation? An Overview of Kerberos Delegation
Kerberos Delegation and Usage Kerberos delegation has been around for a long time (Windows Server 2000 to be exact), but more often than not, when speaking to engineers who manage or work with Active Directory, they’re not familiar with all the various implementations of Kerberos delegation, their uses, and some ways they can be abused. […]
What is Azure Active Directory?
High-Level Overview of Azure AD If you’re reading the Insider Threat Security Blog, I’m sure you’re familiar with Active Directory. We’ve covered many topics with on-premise Active Directory: from clean-up to advanced attacks and threat detection. But what about Azure Active Directory? Has your organization started to march into the cloud and begun the migration […]
Protecting Against DCShadow
What Organizations Can Do to Stop a DCShadow Attack Recently, I came across a post outlining how companies CANNOT effectively defend against a DCShadow attack but instead need to take a reactive approach to identify when it may have occurred by monitoring their environment, and rolling back any unwanted changes once they were identified. Unfortunately, […]
Understanding Passwords and Their Problems
What’s The Problem? Today, with the Internet, social media, personal computers, online banking and everything else that exists, end-users need to create and maintain a large number of usernames and passwords for all of the accounts they have. This begins to create a problem. The many accounts we need to remember leads us to want […]
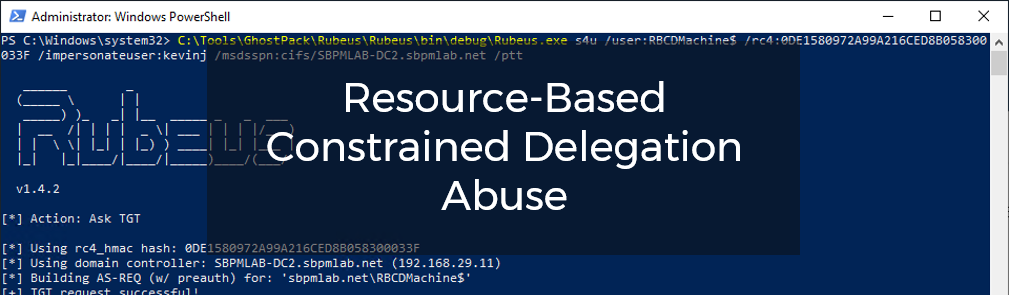
Resource-Based Constrained Delegation Abuse
Abusing RBCD and MachineAccountQuota Delegation is an area that is confusing and complicated for most Active Directory administrators. Unconstrained delegation, constrained delegation, and even resource-based constrained delegation all play a role in not only your Active Directory infrastructure, but also its security posture. For example, unconstrained delegation is very insecure, and can be abused relatively […]

Commando VM: Using the Testing Platform
Windows Offensive VM from Mandiant FireEye Previously, I wrote a high-level overview of the testing platform Commando VM and an installation guide to get started with it. Today, I’ll be diving into a proof of concept of sorts to show off some of the tools and flexibility that the testing platform offers. My goal with […]
Subscribe
DON'T MISS A POST. SUBSCRIBE TO THE BLOG!
© 2022 Stealthbits Technologies, Inc.
