- Solutions
- Products
- StealthAUDITReporting & Governance
- ---
- Stealthbits App Catalog Browse our catalog of no-charge resource connectors, report packs, and more.
- ---
- StealthDEFENDThreat Detection & Response
- ---
- SbPAMPrivileged Access Management
- ---
- StealthINTERCEPTPolicy Enforcement
- ---
- StealthRECOVERRoll Back & Recovery
- StealthAUDIT
- Support
- Partners
- Company
- Resources
- Login
- Free Trial
PROTIP: How to Update the “Have I Been Pwned” (HIBP) Breach Dictionary in StealthINTERCEPT Enterprise Password Enforcer and StealthAUDIT

ALERT: If you are NOT a StealthINTERCEPT Enterprise Password Enforcer or StealthAUDIT customer, view this blog for greater relevance and a more appropriate read.
With 34% of people saying they share passwords with coworkers1 and 62% reusing the same password for work and personal accounts2, the importance of checking passwords is paramount.
Last Friday (June 19, 2020) we saw our first update to the “Have I Been Pwned” (HIPD) database in almost 12 months. The database jumped from 555,278,657 to 572,611,621, an increase of 17.3 Million or 3%. I am not shocked that “123456” is even more popular today, being detected 23,597,311 times. My favorites, “p@ssw0rd” and “P@ssw0rd” have been used 53,154 and 54,230 times respectively.
Maybe more importantly are the ones that are seen less frequently:
- 90% (515 Million) of passwords have been seen 6 or fewer times
- 95% (544 Million) of passwords have been seen 11 or fewer times
- 99% (566 Million) of passwords have been seen 40 or fewer times
Regardless how often they are used, it only takes one to impersonate the right user and you’re breached.
Both StealthINTERCEPT Enterprise Password Enforcer and StealthAUDIT leverage the HIPB database to audit and prevent known bad passwords from being used within Active Directory. Adding these 17 million new passwords enables Stealthbits to provide better password security.
Update Instructions
If the server that you have StealthINTERCEPT Enterprise Password Enforcer installed on has internet access, follow the instructions below.
1. Launch the StealthINTERCEPT Console.
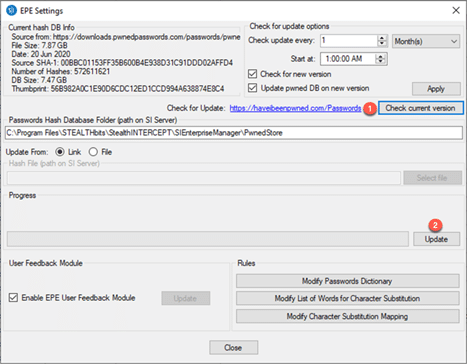
2. Navigate to “Configuration” then “EPE Settings“.
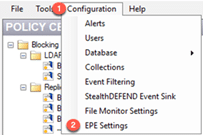
3. Click “Check current version” (This validates a new version is available). Click “Update“.
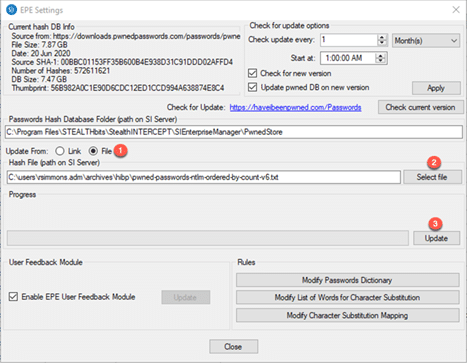
If the server that you have StealthINTERCEPT Enterprise Password Enforcer installed on does not have internet access, follow instructions below.
1. Launch the StealthINTERCEPT Console.
2. Navigate to “Configuration” then “EPE Settings“.
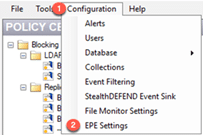
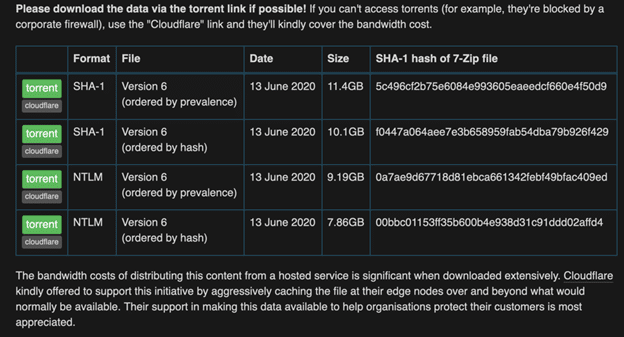
3. Open a web browser and navigate to: https://haveibeenpwned.com/Passwords
Download NTLM Ordered by hast the last option. Uncompress the file using 7zip or tool of your choice.
4. Select “File” as the option for “Update from“. Click “Select File” and browse to the uncompressed file. Click “Update“.
Update Instructions

Follow the instructions below to update StealthAUDIT.
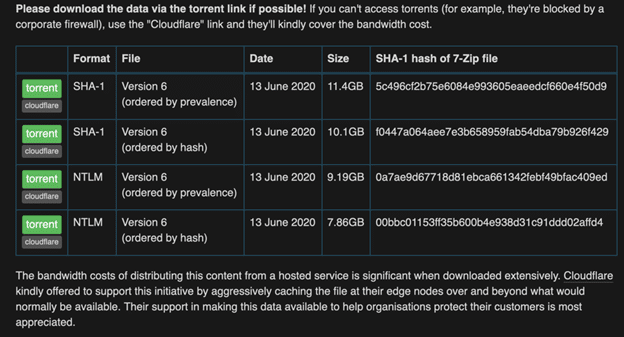
1. Open a web browser and navigate to https://haveibeenpwned.com/Passwords
2. Download NTLM Ordered by hash the last option. Uncompress the file using 7zip or another tool of your choice.
3. Open the StealthAUDIT Windows Console
4. Navigate to the “WeakPasswords” job (Jobs -> Active Directory -> Users -> AD_WeakPasswords
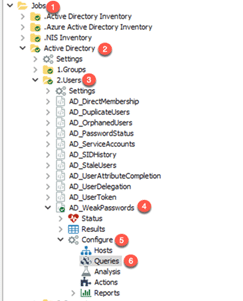
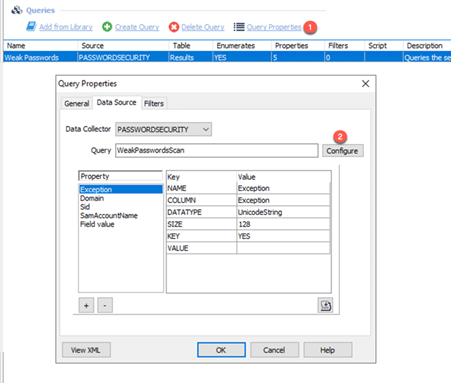
5. Expand the weak passwords job and navigate to “Queries” (AD_WeakPasswords -> Configure -> Queries). Click “Configure“
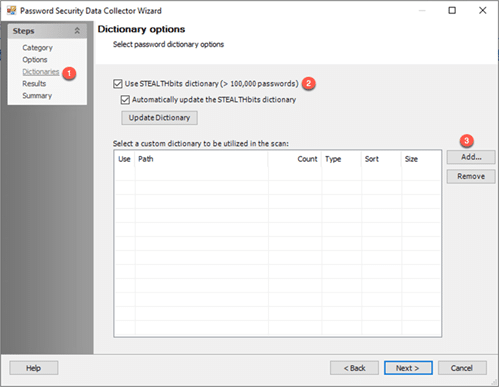
6. Click “Dictionaries“. If you plan to use the HIBP database then you can uncheck the option for Use Stealthbits dictionary as it is a subset of the HIBP database.
Click “Add” and Navigate to your previously downloaded and uncompressed HIBP file.
1https://www.surveymonkey.com/curiosity/why-people-share-passwords-with-coworkers/

Rod Simmons is VP of Product Strategy at STEALTHbits Technologies responsible for the vision and strategy of their Active Directory Management and Security solutions. Rod has been in the technology space for over 20 years.
Prior to joining STEALTHbits, he served as Director of Product Management at BeyondTrust responsible for the Privileged Access Management products. He has also held positions leading Solution Architects and Product Managers at Quest Software and Netpro Computing Inc.
Related Posts
- PROTIP – How to Purge Data in StealthAUDIT
- PROTIP – Fulfill a DSAR with StealthAUDIT 11.0
- Best Practices – Setting up StealthAUDIT SQL Server Database
- ProTip: How to Setup User Activity & Server Logon Scan in StealthAUDIT for Oracle
- Pro Tip – StealthINTERCEPT DB Maintenance Best Practices
- PROTIP: Policy Registration & Managing StealthINTERCEPT via PowerShell and Editing StealthDEFEND Investigations & Categorizing Playbooks
- Protip: How to Setup User Activity & Database Logon Scans in StealthAUDIT for Oracle
- ProTip – The Power of Character Substitution Checks in StealthINTERCEPT Enterprise Password Enforcer
- Protip: How to Setup User Activity & Server Logon Scan in StealthAUDIT for SQL
- ProTip: Exciting New StealthDEFEND Functionality Available with the Release of Version 2.2 on November 5, 2019
Featured Asset
Stealthbits Credential and Data Security Assessment
Proper data security begins with a strong foundation. Find out what you're standing on with a free deep-dive into the security of your Structured and Unstructured Data, Active Directory, and Windows infrastructure.
Read moreSubscribe
DON’T MISS A POST. SUBSCRIBE TO THE BLOG!
© 2022 Stealthbits Technologies, Inc.

Leave a Reply