- Solutions
- Products
- StealthAUDITReporting & Governance
- ---
- Stealthbits App Catalog Browse our catalog of no-charge resource connectors, report packs, and more.
- ---
- StealthDEFENDThreat Detection & Response
- ---
- SbPAMPrivileged Access Management
- ---
- StealthINTERCEPTPolicy Enforcement
- ---
- StealthRECOVERRoll Back & Recovery
- StealthAUDIT
- Support
- Partners
- Company
- Resources
- Login
- Free Trial
StealthAUDIT 8.0: Active Directory Permissions Analyzer

Active Directory Permissions
The release of StealthAUDIT 8.0 delivers enhanced Active Directory (AD) Permissions analysis capabilities. This is welcome news to the over 90% of organizations that use Active Directory to control who can access their network and resources. I say welcome because there are so many different ways to grant privileged access to AD and no easy way to see all these permissions in one place with native tools.
Permissions Analyzer
That’s where comes StealthAUDIT for Active Directory – Permissions Analyzer comes in. Using Permissions Analyzer’s comprehensive, preconfigured analyses and reports, administrators can automatically determine effective permissions associated with Active Directory domains, organizational units (OUs), groups, users, and computers. Customers who have already started using Permissions Analyzer tell us it gives them the most authoritative view of who has permissions to critical objects within AD. 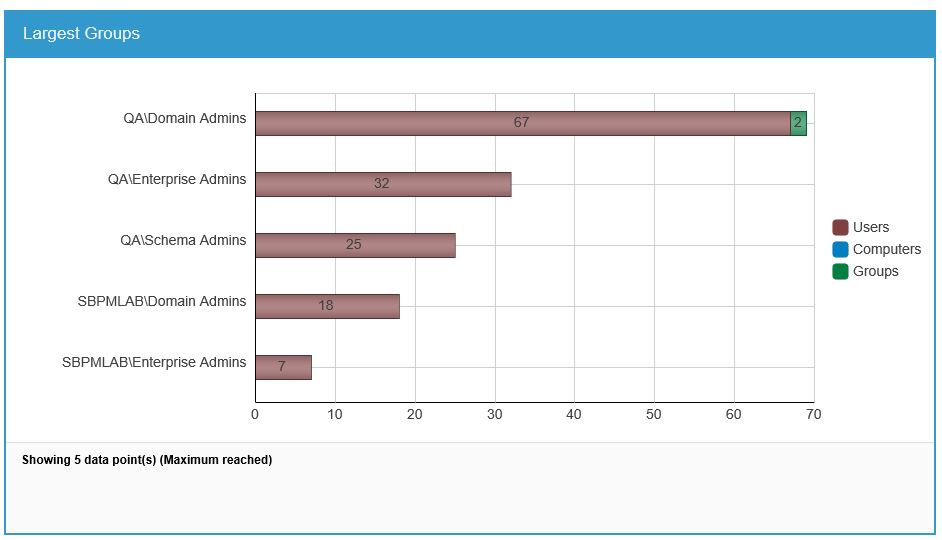
Active Directory Permissions Auditing and Reporting
Here is an overview of Active Directory Permissions Analyzer’s key features:
- Reset Password – Highlight instances where “Reset Password” permissions are applied to Active Directory user objects, with information summarized at the domain and enterprise levels.

- User Permissions – Pinpoint places where permissions are applied to Active Directory user objects, as well as the level of permissions granted (e.g. read, write, and delete).
- Group Membership – Know which trustees can change the membership of Active Directory group objects, either by writing the member attribute or via the “Add/Remove self as member” permission.
- Group Permissions – Understand where permissions are applied to Active Directory group objects to shed light on who can perform critical operations against AD groups.
- Organizational Unit (OU) Permissions – Analyze and report on where permissions are applied to Active Directory OUs, with the information summarized at the domain and enterprise levels.
- Computer Permissions – Uncover instances where permissions are applied to Active Directory computer objects to avoid breach scenarios.
- Open Access by Domain – Discover instances of open access on Active Directory objects like Domain Users, Authenticated Users, and Everyone and summarize findings by domain.
- Broken Inheritance by Domain – Gain insight into instances of broken inheritance on Active Directory objects, showing where the inheritance has been broken, regardless of location in the permissions tree.
To download a free trial of Permissions Analyzer, please click here.
Don’t miss a post! Subscribe to The Insider Threat Security Blog here:

Tuula Fai is the Senior Marketing Director of StealthAUDIT at STEALTHbits. For the past 20 years, she has worked in a variety of roles within the software industry, starting as a developer and implementation engineer before moving into product marketing and digital campaigns. Having worked in both customer service and human resources, she is passionate about safeguarding customer and employee data as part of overall security initiatives. She graduated Summa cum Laude from Georgetown with an MBA in marketing and IT, and has won two technology marketing awards. You can find her running and writing in the Rocky Mountains of Colorado.
Related Posts
- Sensitive Data Discovery for Compliance
- Using The Azure Information Protection (AIP) Scanner to Discover Sensitive Data
- Advanced Data Security Features for Azure SQL- Part 1: Data Discovery & Classification
- How to Protect Office 365 by Classifying Your Data with Microsoft’s AIP Labels
- 2019 Verizon DBIR Key Findings
- 5 Cybersecurity Trends for 2019
- EU GDPR: Paving the Way for New Privacy Laws?
- Announcing Stealthbits Activity Monitor 3.0 & StealthINTERCEPT 5.1
- Key Take Aways from the Ponemon 2018 Cost of Insider Threats Report
- Where Real Organizations Are with EU GDPR 10 Days from Launch
Featured Asset
Stealthbits Credential and Data Security Assessment
Proper data security begins with a strong foundation. Find out what you're standing on with a free deep-dive into the security of your Structured and Unstructured Data, Active Directory, and Windows infrastructure.
Read moreSubscribe
DON’T MISS A POST. SUBSCRIBE TO THE BLOG!
© 2022 Stealthbits Technologies, Inc.

Leave a Reply