- Solutions
- Products
- StealthAUDITReporting & Governance
- ---
- Stealthbits App Catalog Browse our catalog of no-charge resource connectors, report packs, and more.
- ---
- StealthDEFENDThreat Detection & Response
- ---
- SbPAMPrivileged Access Management
- ---
- StealthINTERCEPTPolicy Enforcement
- ---
- StealthRECOVERRoll Back & Recovery
- StealthAUDIT
- Support
- Partners
- Company
- Resources
- Login
- Free Trial
What is the NYDFS Cybersecurity Regulation?

The New York Department of Financial Services released the NYDFS Cybersecurity Regulation (23 NYCRR 500) in 2017, a set of regulations that place cybersecurity requirements on all DFS regulated entities. This regulation was put into effect at a time where cybersecurity threats are growing, with players coming from nation-states such as Russia, to independent criminal actors, or even terrorist organizations. The goal of this regulation is to not only protect customer information but to also protect a company’s own assets.
Who Must Comply with the NYDFS Cybersecurity Regulation?

The NYDFS supervises several different types of institutions to varying degrees including chartering, licensing, registration or filing requirements, and examination. The list below displays various types of covered entities.
- Bank Trust Companies
- Charitable Foundations
- Credit Unions
- Foreign Bank Offices
- Investment Companies
- Licensed Lenders
- Life Insurance Companies
- Mortgage Brokers
- Private Bankers
- Savings Banks
For a complete list of covered entities, visit the NYDFS Who We Supervise page.
Exemptions exist for companies that fall under the following categories:
- Has less than 10 employees
- Earns less than $5,000,000 in gross annual revenue in each of the last 3 fiscal years
- Has less than $10,000,000 in year-end total assets
- Does not directly or indirectly control, own, access, generate, receive or possess Nonpublic Information other than information relating to its corporate parent company
How to Comply with the NYDFS Cybersecurity Regulations
The regulation imposed by the NYDFS requires each company to assess its specific risks and design a security program accordingly. The key pieces of the regulation include:
- Designate a Chief Information Security Officer (CISO) to be responsible for overseeing and implementing the determined cybersecurity program.
- Periodic Risk Assessments to inform the design of the cybersecurity program which should be updated as necessary to address changes to the company’s information systems, non-public information, or business operations (Section 500.09)
- Appropriate Policies to address areas such as information security, data governance and classification, data privacy, incidence response, and more (Section 500.03)
- A complete Audit Trail of incidences and responses for no fewer than five years (Section 500.06)
- Limit Access Privileges to Nonpublic information, and periodically review such access (Section 500.07)
- Leverage Multi-Factor Authentication where applicable to prevent unauthorized access to Nonpublic Information (Section 500.12)
- Annual Penetration Testing based on relevant risks identified within the risk assessment (Section 500.05)
- Annual Notices to the Superintendent certifying that the company is in compliance with the requirements set forth in the regulation. Additionally, notices must also be provided in the case that an event has occurred that may cause harm to regular operation, or must otherwise be reported to any government body, self-regulatory agency, or any other supervisory body (Section 500.17)
Notable Dates and Timelines
- March 1, 2017 – Regulation went into effect.
- August 28, 2017 – 180 days after the regulation went into effect, indicating all covered entities must be in compliance with the requirements unless otherwise specified.
- February 15, 2018 – First Certification of Compliance submitted to the superintendent.
- March 1, 2018 – 1 year after the regulation went into effect, indicating all covered entities must be in compliance with the requirements of sections 500.04(b), 500.05, 500.09, 500.12, and 500.14(b).
- September 1, 2018 – 18 months after the regulation went into effect, indicating all covered entities must be in compliance with the requirements of sections 500.06, 500.08, 500.13, 500.14 (a) and 500.15.
- March 1, 2019 – 2 years after the regulation went into effect, indicating all covered entities must be in compliance with the requirements of section 500.11.
Best Practices for Compliance
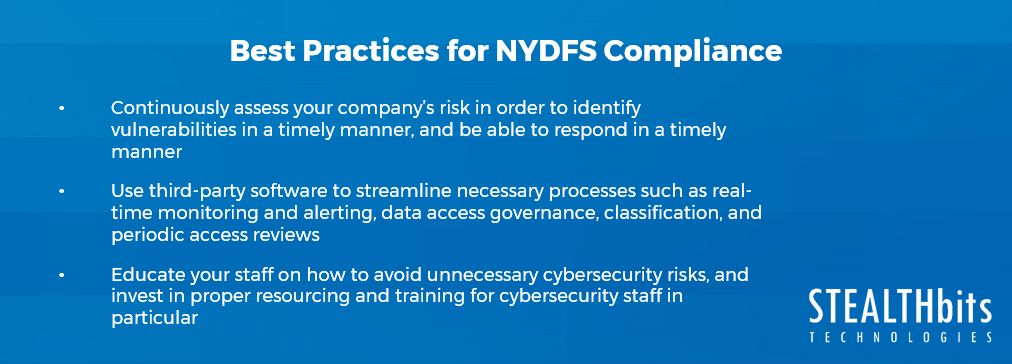
The clock has already started clicking, and by this point, you should be compliant if you are considered a covered entity under the NYDFS. There are several things that should’ve happened already, and things that should continue to happen to stay within compliance:
- Continuously assess your company’s risk in order to identify vulnerabilities in a timely manner, and be able to respond in a timely manner.
- Use third-party software to streamline necessary processes such as real-time monitoring and alerting, data access governance, classification, and periodic access reviews.
- Educate your staff on how to avoid unnecessary cybersecurity risks, and invest in proper resourcing and training for cybersecurity staff in particular. As stated in the regulation, the number of cyber events has been steadily increasing and with that is the risk to the financial services industry. It will be integral to ensure cyber staff is up to date with the latest cybersecurity risks and trends.

Farrah Gamboa is a Director of Technical Product Management at Stealthbits – now part of Netwrix. She is responsible for building and delivering on the roadmap of Stealthbits products and solutions.
Since joining Stealthbits in 2012, Farrah has held multiple technical roles, including Scrum Master and Quality Assurance Manager. Farrah holds a Bachelor of Science degree in Industrial Engineering from Rutgers University
Related Posts
- 3 Strategies to Ensure Readiness for DSARs
- Global Compliance Demands: The Singaporean Personal Data Protection Act (PDPA) Reviewed
- South Africa’s Protection of Personal Information Act (POPIA) Compliance
- Lei Geral de Proteção de Dados Pessoais (LGPD Compliance) – What You Need to Know About Brazil’s National Data Privacy Regulation
- What is the California Privacy Rights Act?
- What is a Data Protection Impact Assessment (DPIA)?
- EU-US Privacy Shield Revoked: What This Means for EU-US Commercial Data Transfers
- Key Requirements of the NY SHIELD Act and How to be Compliant
- What is the California Consumer Privacy Act (CCPA)?
- What is APRA’s CPS 234? Part 2
Featured Asset
Stealthbits Credential and Data Security Assessment
Proper data security begins with a strong foundation. Find out what you're standing on with a free deep-dive into the security of your Structured and Unstructured Data, Active Directory, and Windows infrastructure.
Read moreSubscribe
DON’T MISS A POST. SUBSCRIBE TO THE BLOG!
© 2022 Stealthbits Technologies, Inc.

Leave a Reply